Secure Software Development Lifecycle SSDLC Guide
Introduction
The Secure Software Development Lifecycle (SSDLC) is a process that integrates security practices into every phase of software development—from planning and design to coding, testing, and deployment. Unlike traditional development models that treat security as an afterthought, SSDLC ensures that applications are built with security in mind from the very beginning.
For Pakistani students, learning an ssdlc tutorial is especially important in today’s digital landscape. With the rise of fintech startups in Karachi, e-commerce platforms in Lahore, and government digitalization initiatives in Islamabad, secure applications are no longer optional—they are essential. Cyberattacks such as data breaches, ransomware, and API abuse are increasing, and developers must be prepared to defend against them.
By mastering SSDLC, you will:
- Build secure applications from day one
- Reduce the cost of fixing vulnerabilities later
- Improve job prospects in cybersecurity and software engineering
Prerequisites
Before starting this guide, you should have:
- Basic programming knowledge (JavaScript, Python, or Java)
- Understanding of web development (frontend + backend basics)
- Familiarity with Git and version control
- Basic knowledge of cybersecurity concepts (e.g., authentication, encryption)
- Awareness of common vulnerabilities (like SQL Injection, XSS)
Core Concepts & Explanation
Secure Software Development Lifecycle Phases
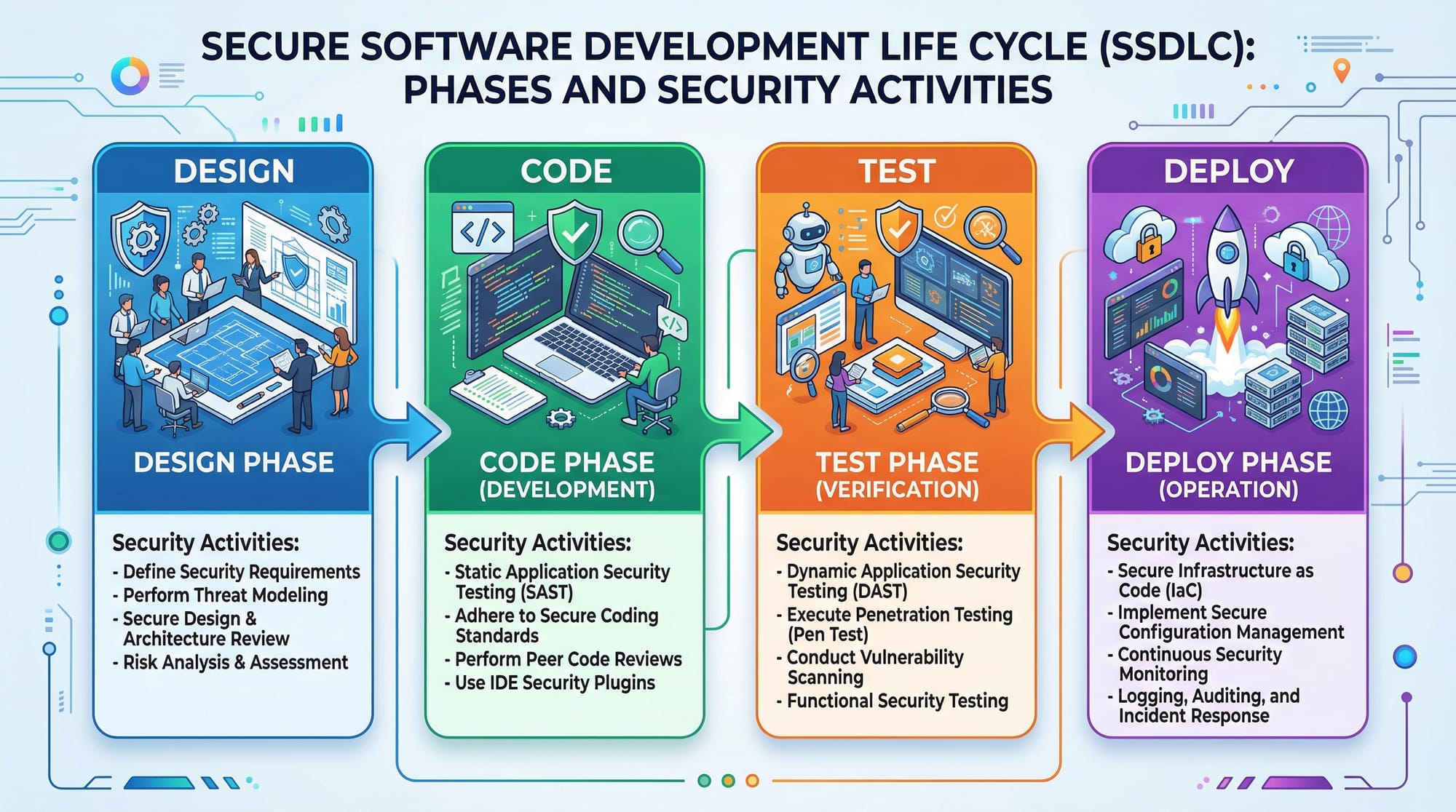
The SSDLC consists of multiple phases, each with embedded security practices:
- Requirements Phase
- Identify security requirements
- Example: A banking app in Pakistan must comply with SBP (State Bank of Pakistan) regulations
- Design Phase
- Perform threat modeling
- Define secure architecture
- Development Phase
- Follow secure coding practices
- Use code reviews and static analysis tools
- Testing Phase
- Conduct security testing (SAST, DAST)
- Identify vulnerabilities before deployment
- Deployment & Maintenance
- Monitor logs
- Apply patches and updates regularly
Example:
Ali is building an e-commerce app in Lahore. Instead of waiting until the end to test security, he integrates validation checks, authentication, and encryption from the start.
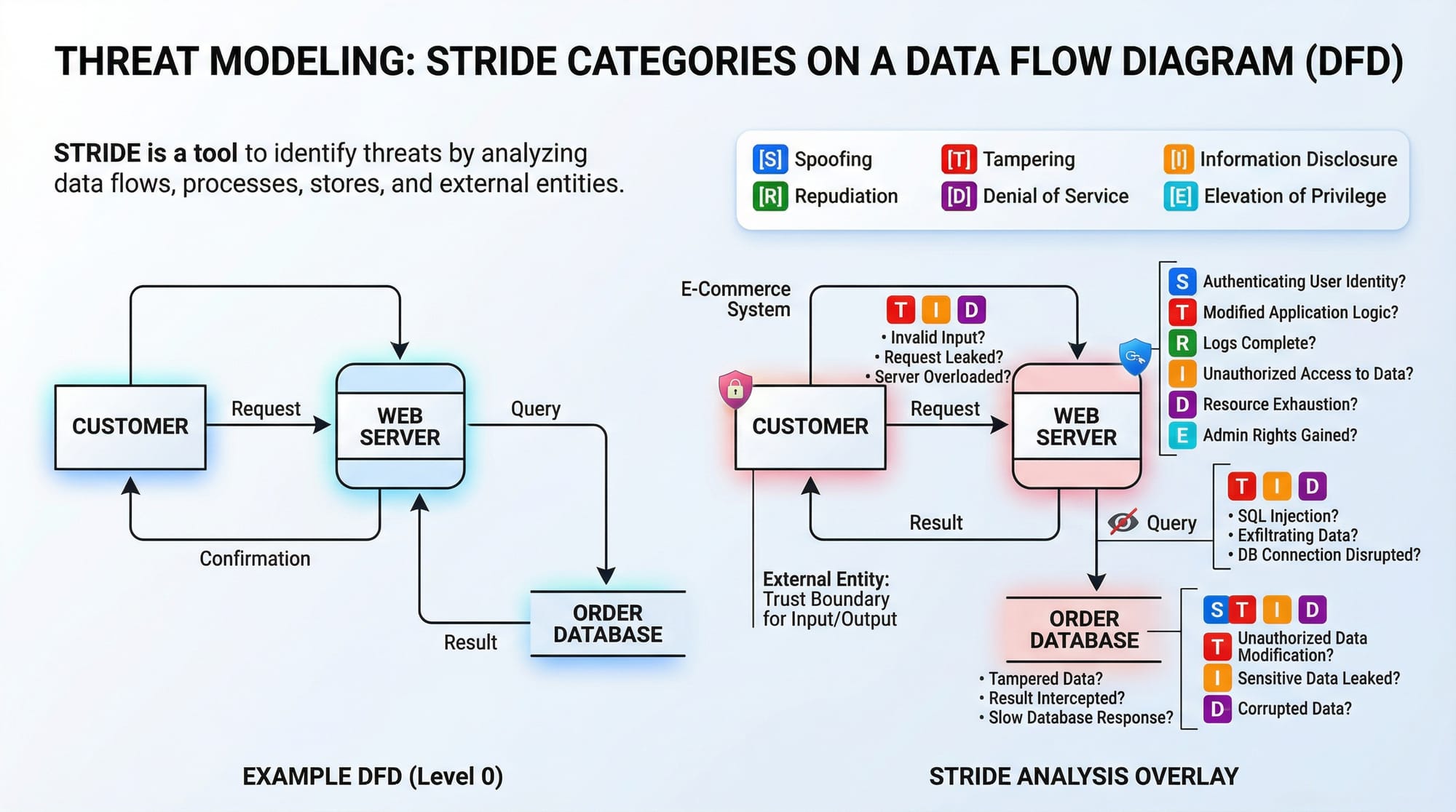
Threat Modeling with STRIDE
Threat modeling helps identify potential risks early in the design phase.
The STRIDE model includes:
- Spoofing (fake identity)
- Tampering (data modification)
- Repudiation (denying actions)
- Information Disclosure (data leaks)
- Denial of Service (DoS attacks)
- Elevation of Privilege (unauthorized access)
Example:
Fatima is designing a login system:
- Spoofing → Fake login attempts
- Tampering → Password changes
- Information Disclosure → Exposing user data
By identifying these threats early, she can design countermeasures.
Practical Code Examples
Example 1: Input Validation to Prevent SQL Injection
// Vulnerable code
const express = require('express');
const app = express();
app.get('/user', (req, res) => {
const username = req.query.username;
const query = "SELECT * FROM users WHERE username = '" + username + "'";
db.query(query, (err, result) => {
res.send(result);
});
});
Explanation (Line-by-Line)
const express = require('express');
Imports Express framework for building web apps.const app = express();
Initializes the Express application.app.get('/user', (req, res) => {
Defines an API endpoint/user.const username = req.query.username;
Takes user input from query parameters (unsafe).const query = ...
Directly inserts user input into SQL query → vulnerable to SQL Injection.db.query(query, ...)
Executes the unsafe query.
Secure Version
// Secure code using parameterized queries
app.get('/user', (req, res) => {
const username = req.query.username;
const query = "SELECT * FROM users WHERE username = ?";
db.query(query, [username], (err, result) => {
res.send(result);
});
});
Explanation
?placeholder prevents SQL injection[username]safely binds user input- Database treats input as data, not executable SQL
Example 2: Real-World Application (Authentication System)
const bcrypt = require('bcrypt');
// Register user
async function registerUser(password) {
const saltRounds = 10;
const hashedPassword = await bcrypt.hash(password, saltRounds);
return hashedPassword;
}
// Login user
async function loginUser(inputPassword, storedHash) {
const match = await bcrypt.compare(inputPassword, storedHash);
return match;
}
Explanation (Line-by-Line)
const bcrypt = require('bcrypt');
Imports hashing library.async function registerUser(password)
Function to handle registration.const saltRounds = 10;
Defines complexity of hashing.await bcrypt.hash(password, saltRounds);
Hashes password securely.loginUser(...)
Compares entered password with stored hash.bcrypt.compare(...)
Prevents storing plain text passwords.
Real-World Context:
Ahmad builds a freelancing platform in Islamabad. By hashing passwords, he protects user accounts even if the database is compromised.
Common Mistakes & How to Avoid Them
Mistake 1: Ignoring Input Validation
Problem:
Developers trust user input.
Example (Bad Code):
const age = req.query.age;
if(age > 18){
// allow access
}
Fix:
const age = parseInt(req.query.age, 10);
if (!Number.isInteger(age)) {
return res.status(400).send("Invalid input");
}
Explanation
parseInt()ensures numeric inputNumber.isInteger()validates type- Prevents injection and logic errors
Mistake 2: Hardcoding Secrets
Problem:
API keys stored in code.
const API_KEY = "12345SECRET";
Fix:
const API_KEY = process.env.API_KEY;
Explanation
- Uses environment variables
- Keeps secrets out of source code
- Safer for GitHub repositories
Practice Exercises
Exercise 1: Fix SQL Injection
Problem:
Convert unsafe query into a secure one.
const query = "SELECT * FROM products WHERE id = " + req.query.id;
Solution:
const query = "SELECT * FROM products WHERE id = ?";
db.query(query, [req.query.id]);
Explanation
- Replaces string concatenation
- Uses parameterized query
- Prevents SQL injection
Exercise 2: Secure Password Storage
Problem:
Store passwords securely.
const password = "mypassword123";
Solution:
const bcrypt = require('bcrypt');
const hash = await bcrypt.hash(password, 10);
Explanation
- Uses hashing instead of plain text
- Protects user data
- Essential for authentication systems
Frequently Asked Questions
What is SSDLC and why is it important?
SSDLC is a process that integrates security into every stage of software development. It helps prevent vulnerabilities early, reducing costs and improving application security.
How do I start learning secure coding practices?
Begin with common vulnerabilities like SQL Injection and XSS, then practice using secure libraries and tools like bcrypt, input validation, and static analysis tools.
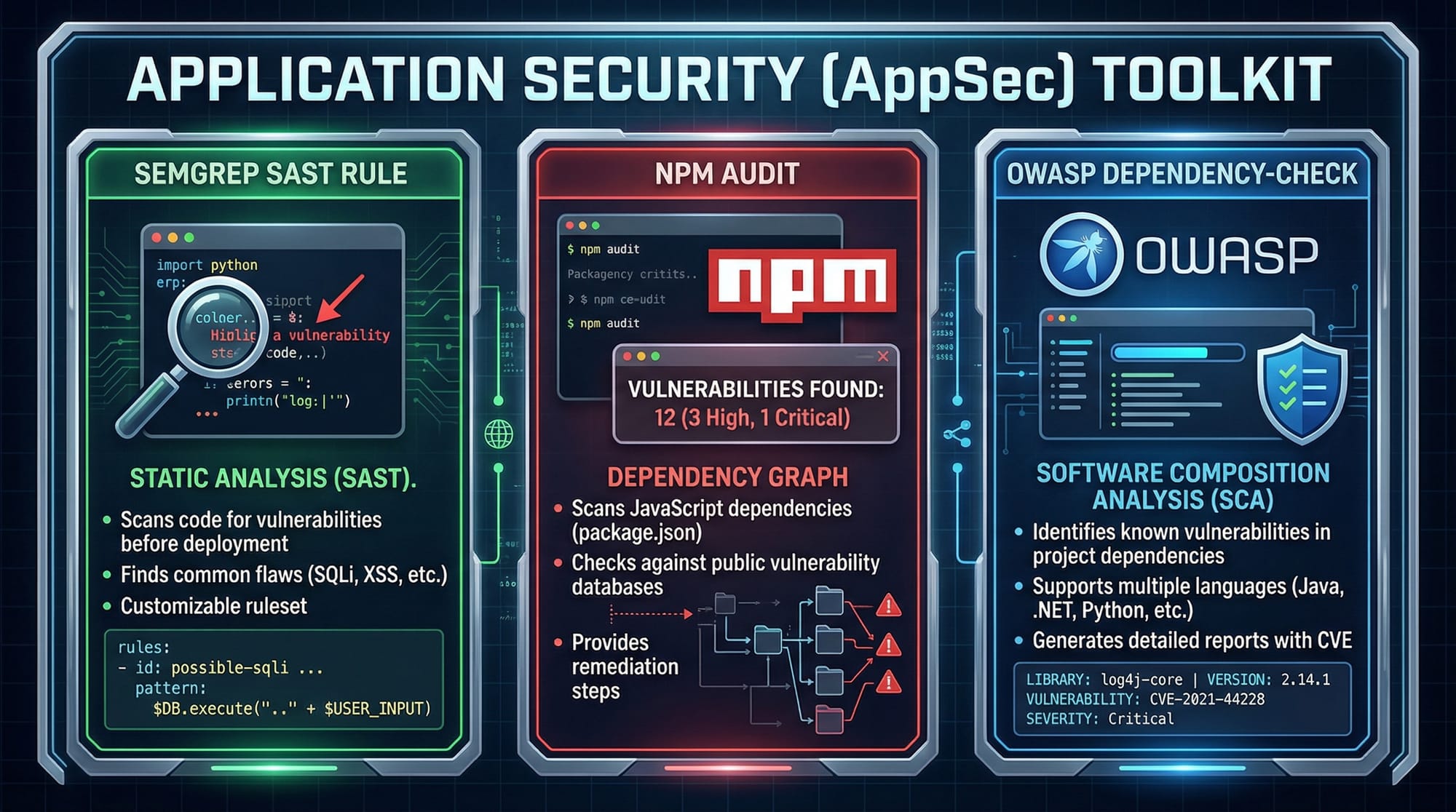
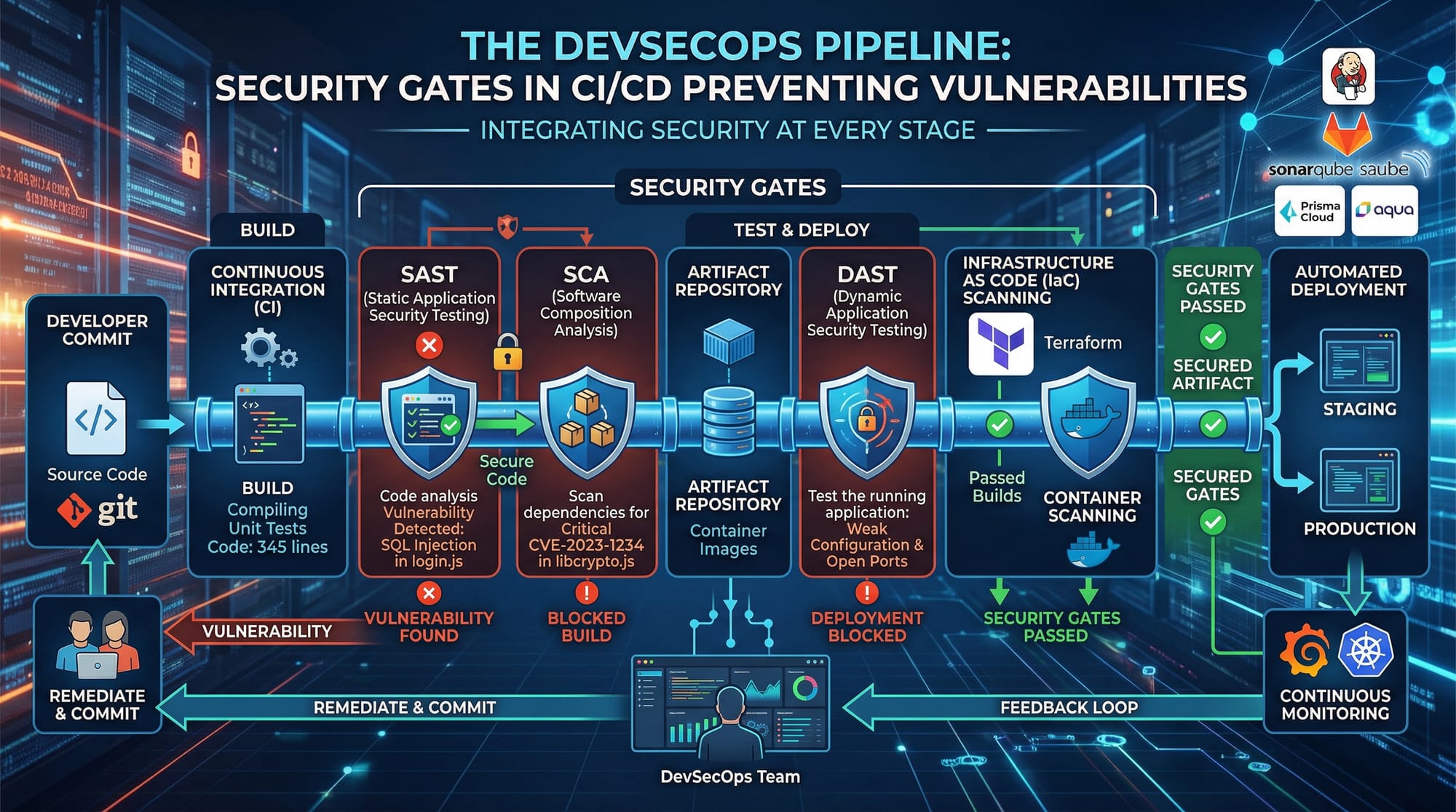
What tools are used in SSDLC?
Popular tools include SAST tools (Semgrep), DAST tools (OWASP ZAP), and dependency scanners like npm audit and OWASP Dependency-Check.
Is SSDLC only for large companies?
No, even small startups in Pakistan can benefit from SSDLC. Implementing basic security practices can prevent major data breaches.
How does SSDLC improve job opportunities?
Employers value developers who understand application security. SSDLC knowledge makes you suitable for roles in cybersecurity, DevSecOps, and secure software engineering.
Summary & Key Takeaways
- SSDLC integrates security into every development phase
- Threat modeling (STRIDE) helps identify risks early
- Secure coding practices prevent common vulnerabilities
- Tools like SAST and DAST enhance application security
- Avoid mistakes like hardcoding secrets and ignoring validation
- Security is essential for modern software development
Next Steps & Related Tutorials
To continue your learning journey on theiqra.edu.pk, explore:
- Learn Docker Security Best Practices to secure containerized apps
- Study the OWASP Top 10 vulnerabilities to understand common risks
- Explore a JWT Security Tutorial for secure authentication
- Dive into a Burp Suite Pentesting Guide to test your applications
By combining SSDLC knowledge with these topics, you’ll build strong expertise in application security and become a highly valuable developer in Pakistan’s growing tech industry 🚀
Test Your Python Knowledge!
Finished reading? Take a quick quiz to see how much you've learned from this tutorial.