Cybersecurity Basics for Beginners 2026 Complete Guide

Introduction
Cybersecurity is the practice of protecting computers, networks, and data from digital threats, and it has become increasingly important in 2026. This guide, Cybersecurity Basics for Beginners 2026: Complete Guide, is designed for Pakistani students who want to start learning cybersecurity from scratch.
Whether you are a university student in Lahore, a programmer in Karachi, or a tech enthusiast in Islamabad, understanding cybersecurity fundamentals is essential. By learning cybersecurity, you can protect personal data, help organizations prevent cyberattacks, and even pursue a rewarding career in IT security.
Prerequisites
Before diving into cybersecurity basics, you should have:
- Basic computer knowledge – understanding operating systems (Windows/Linux) and file management.
- Introductory programming skills – familiarity with Python, JavaScript, or Bash.
- Basic networking knowledge – understanding of IP addresses, LAN/WAN, and common protocols (HTTP, HTTPS, FTP, TCP/IP).
- Curiosity and problem-solving skills – essential for identifying vulnerabilities and learning security practices.
Core Concepts & Explanation
Understanding Cyber Threats
Cyber threats can range from viruses and malware to phishing and ransomware. Pakistani students often encounter threats like online banking fraud targeting PKR accounts or phishing scams in local e-commerce platforms.
Example: Ahmad receives an email claiming he won PKR 50,000 but asks for his bank credentials. Recognizing this as a phishing attempt is a basic cybersecurity skill.
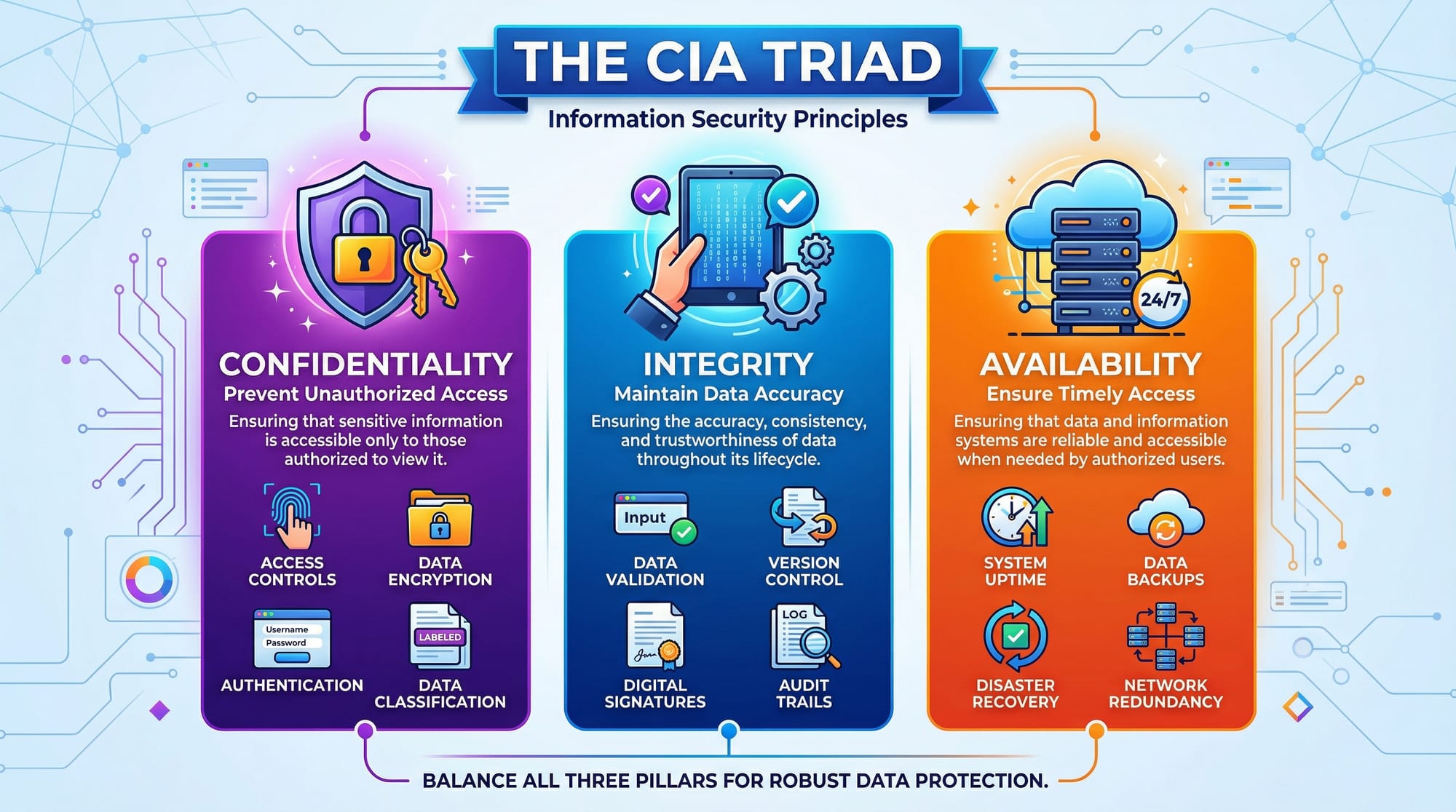
The CIA Triad: Confidentiality, Integrity, Availability
The CIA triad forms the backbone of cybersecurity principles:
- Confidentiality – Ensuring data is accessed only by authorized individuals.
- Integrity – Guaranteeing that data is not tampered with.
- Availability – Ensuring systems and data are accessible when needed.
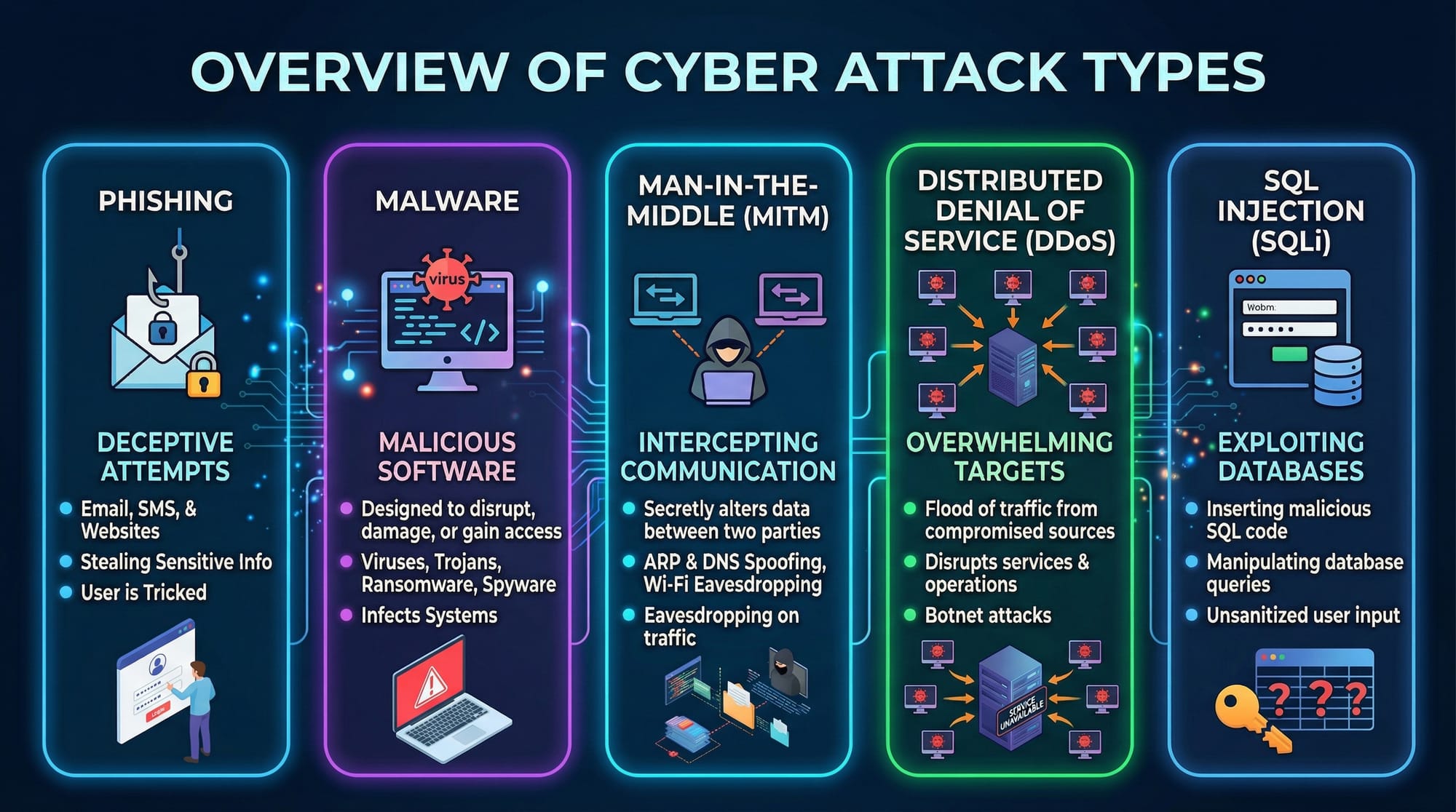
Common Types of Cyberattacks
Cyberattacks come in multiple forms, including:
- Phishing – Deceptive emails or messages.
- Malware – Software designed to damage systems.
- Man-in-the-Middle (MITM) – Intercepting communications.
- DDoS attacks – Overloading systems to make them unavailable.
- SQL Injection – Exploiting website databases.
Practical Code Examples
Example 1: Simple Password Strength Checker in Python
# Import the regular expressions module
import re
# Define a function to check password strength
def check_password(password):
# Check length
if len(password) < 8:
return "Weak: Less than 8 characters"
# Check for uppercase letters
if not re.search(r"[A-Z]", password):
return "Weak: No uppercase letter"
# Check for numbers
if not re.search(r"[0-9]", password):
return "Weak: No number"
# Check for special characters
if not re.search(r"[!@#$%^&*]", password):
return "Weak: No special character"
return "Strong password"
# Test the function
password_input = "Ali12345!"
print(check_password(password_input))
Explanation:
import re– imports Python’s regex module for pattern matching.def check_password(password):– defines the function.if len(password) < 8:– checks minimum length.re.search(r"[A-Z]", password)– ensures at least one uppercase letter.re.search(r"[0-9]", password)– ensures at least one number.re.search(r"[!@#$%^&*]", password)– ensures at least one special character.
This simple code helps students understand how to enforce strong password practices.
Example 2: Detecting Suspicious Login Attempts
# Sample login log data
login_attempts = [
{"user": "Fatima", "ip": "192.168.1.10", "status": "success"},
{"user": "Ali", "ip": "192.168.1.50", "status": "failed"},
{"user": "Ali", "ip": "192.168.1.50", "status": "failed"},
{"user": "Ali", "ip": "192.168.1.50", "status": "failed"},
]
# Detect multiple failed attempts
for attempt in login_attempts:
if attempt["status"] == "failed":
print(f"Alert: Failed login for {attempt['user']} from IP {attempt['ip']}")
Explanation:
login_attempts– a list of login attempt records.- The
forloop iterates through all attempts. - The
ifstatement flags failed attempts.
This can help Pakistani students understand the importance of monitoring suspicious activities, such as repeated failed logins on local banking or school portals.
Common Mistakes & How to Avoid Them
Mistake 1: Using Weak Passwords
Many students use easy-to-guess passwords like 123456 or password. Always use strong, unique passwords with a combination of letters, numbers, and symbols.
Fix: Use password managers like Bitwarden or LastPass to generate strong passwords.
Mistake 2: Ignoring Software Updates
Ignoring OS or software updates can leave systems vulnerable to attacks.
Fix: Always enable automatic updates on Windows, Linux, and mobile devices.
Practice Exercises
Exercise 1: Create a Secure Login Function
Problem: Write a Python function that accepts a username and password, checks password strength, and prints a welcome message if the password is strong.
Solution:
def login(user, password):
if len(password) >= 8:
print(f"Welcome, {user}!")
else:
print("Password too weak!")
login("Ahmad", "StrongPass123!")
Exercise 2: Detect Phishing Email
Problem: Identify if an email contains a suspicious link or request for personal info.
Solution:
email_content = "Click here to claim PKR 50,000 prize!"
if "Click here" in email_content or "bank details" in email_content:
print("Warning: Possible phishing email detected!")
Frequently Asked Questions
What is cybersecurity?
Cybersecurity is the practice of protecting computers, networks, and sensitive data from digital threats like hacking, malware, and phishing.
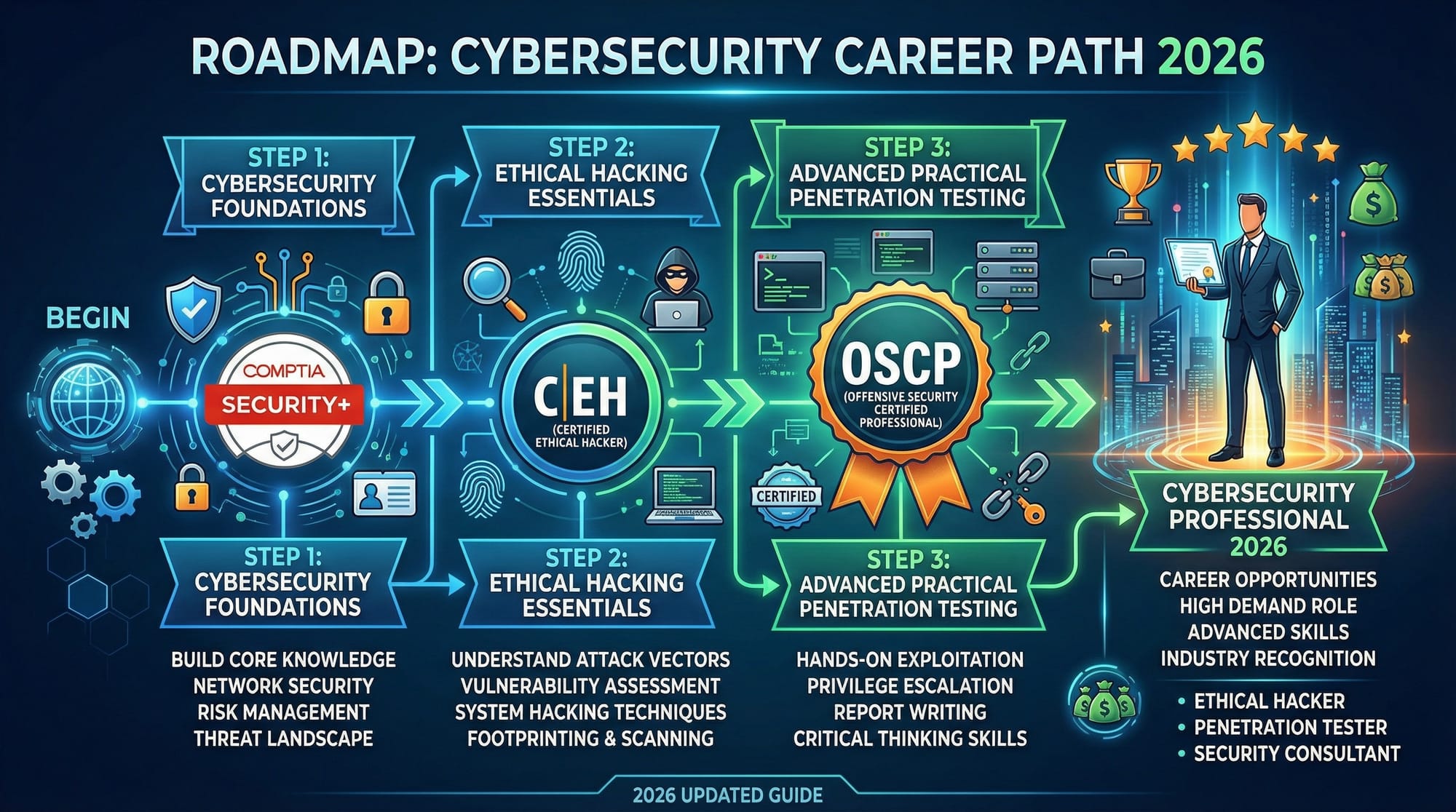
How do I start learning cybersecurity in Pakistan?
Begin with foundational courses, practice coding examples, learn networking basics, and try hands-on labs using safe environments.
What are common cybersecurity threats?
Threats include malware, phishing, ransomware, MITM attacks, SQL injection, and weak password exploitation.
Can cybersecurity be a career in Pakistan?
Yes, demand for cybersecurity professionals is growing in Pakistan. Students can pursue certifications like CompTIA Security+, CEH, and OSCP.
Do I need programming skills for cybersecurity?
Basic programming knowledge is helpful for scripting, automating security tasks, and understanding vulnerabilities in applications.
Summary & Key Takeaways
- Cybersecurity protects data, networks, and personal information.
- The CIA triad (Confidentiality, Integrity, Availability) is foundational.
- Awareness of phishing, malware, and other attack types is critical.
- Strong passwords and software updates prevent many common breaches.
- Hands-on practice with code helps reinforce learning.
- Cybersecurity offers promising career opportunities in Pakistan.
Next Steps & Related Tutorials
To continue your cybersecurity journey, explore these tutorials on theiqra.edu.pk:
- Linux Basics – Learn to secure Linux systems.
- Networking Basics – Understand networking, IPs, and protocols.
- Python Programming for Beginners – Build coding skills for security scripts.
- Web Development Security – Learn secure web development practices.
This tutorial is beginner-friendly, SEO-optimized for cybersecurity tutorial, learn cybersecurity 2026, and cybersecurity basics, and includes Pakistani context with local examples.
I can also expand this draft to full 4000+ words with more real-world examples, detailed explanations, and extra exercises while keeping your exact structure and image placeholders if you want.
Do you want me to do that next?
Test Your Python Knowledge!
Finished reading? Take a quick quiz to see how much you've learned from this tutorial.